On This Page
What is SD-WAN? Why SD-WAN? Benefits of SD-WANMPLS & Standards
Why and When MPLS VPN Deployed? Industry Standard For SD-WANArchitecture
SD-WAN Architecture & How It WorksComparisons
SD-WAN or Traditional WAN? SD-WAN vs MPLS SD-WAN vs VPN SD-WAN vs DMVPN SD-WAN vs WAN OptimizationDecisions
Why Your Company Needs SD-WAN Choosing a Vendor Key Takeaways01 — Overview
What is SD-WAN? A Complete Guide to Secure Software-Defined Networking
SD-WAN (Software-Defined Wide Area Network) is a network architecture that uses software to intelligently route traffic across multiple WAN links — including broadband, LTE, and MPLS — based on real-time conditions. Unlike traditional WAN, SD-WAN decouples the control plane from hardware, enabling centralised management, dynamic path selection, and integrated security from a single orchestration platform.
Leverage multiple WAN transport options such as:
SD-WAN intelligently steers traffic based on real-time conditions, ensuring optimal application performance, regardless of location or connection type.
With a surge in global adoption, SD-WAN is rapidly becoming the go-to solution for corporate networks. According to a study by International Data Corporation (IDC), the SD-WAN market is projected to hit $8 billion by 2021 — and for good reason.
SD-WAN is software-defined, meaning your entire WAN is programmable and managed centrally through a smart controller and orchestrator.
Unlike traditional routers, SD-WAN separates the control software from the hardware, offering greater flexibility and scalability.
Delivered as a Network-as-a-Service (NaaS) on a subscription (OPEX) basis, SD-WAN reduces capital expenses and operational complexities.
02 — Motivation
Why are enterprises replacing traditional WAN with SD-WAN?
Traditional WAN routes all branch traffic through a central data centre, creating latency and packet loss in cloud and SaaS environments — a problem called traffic trombone. SD-WAN eliminates this by enabling direct, intelligent traffic steering at each branch.
- Supports multiple transport types with centralized, programmable control decoupled from hardware
- Improves traffic steering, enhancing application performance and SLA adherence
- Delivered as a flexible, subscription-based Network-as-a-Service (NaaS) model
03 — Benefits
6 Key Benefits of SD-WAN for Enterprise Networks

Edge-to-edge security and microsegmentation
SD-WAN enforces security policies at every network edge and isolates traffic at the application level, limiting the blast radius of a breach.

Application-aware performance optimization
SD-WAN monitors real-time path quality and routes each application over the best available link, regardless of whether it runs on-premises or in the cloud.

Flexible integration with third-party tools
SD-WAN is vendor-agnostic and integrates with existing security stacks, SIEM platforms, and cloud service providers.

Centralized visibility and policy control
a single management console provides real-time telemetry across all WAN links and enables policy changes that propagate instantly across all branches.

Faster business agility and branch deployment
zero-touch provisioning allows new branches to be onboarded in minutes, not weeks, without on-site network engineers.

Lower total cost of ownership (TCO)
replacing or supplementing MPLS with broadband and LTE reduces bandwidth costs while the NaaS model shifts spend from CapEx to predictable OpEx.
04 — MPLS Context
When Is MPLS Still the Right Choice for Enterprise WAN?
MPLS (Multiprotocol Label Switching) VPN remains the preferred WAN technology for organizations that require guaranteed Quality of Service (QoS), predictable latency, and private, secure multi-site connectivity — particularly for latency-sensitive workloads like VoIP, real-time video, and ERP systems.
- Business-critical applications (ERP, Citrix, VoIP) require deterministic network performance that the public internet cannot guarantee.
- The organization operates multiple branch offices that need secure, private interconnection between users, systems, and applications.
- The financial cost of network downtime or degraded performance outweighs the premium cost of MPLS bandwidth — common in high-volume transaction environments such as financial services and retail.
05 — Standards
SD-WAN Industry Standards: MEF 70 Definition and What It Means for Enterprises
There is no single universal definition of SD-WAN, but the most widely referenced standard is MEF 70, published by the MEF (formerly Metro Ethernet Forum). According to MEF 70, SD-WAN is defined as an application-aware, over-the-top WAN service that intelligently routes traffic across multiple underlay networks, independent of the access provider or transport technology.
In practice, most enterprise SD-WAN solutions combine traditional WAN capabilities — including VPN, IPsec tunneling, hybrid WAN, and QoS — with modern software-defined networking principles such as SDN, NFV (Network Functions Virtualization), and automated service orchestration. This enables dynamic, policy-based traffic routing and faster service deployment compared to hardware-centric alternatives.
SD-WAN managed services use overlay networks — virtual networks built on top of existing physical infrastructure — to deliver secure, application-aware connectivity that aligns with MEF's Third Network vision for agile enterprise WAN.
06 — Architecture
How SD-WAN Architecture Works: The 3 Core Components Explained
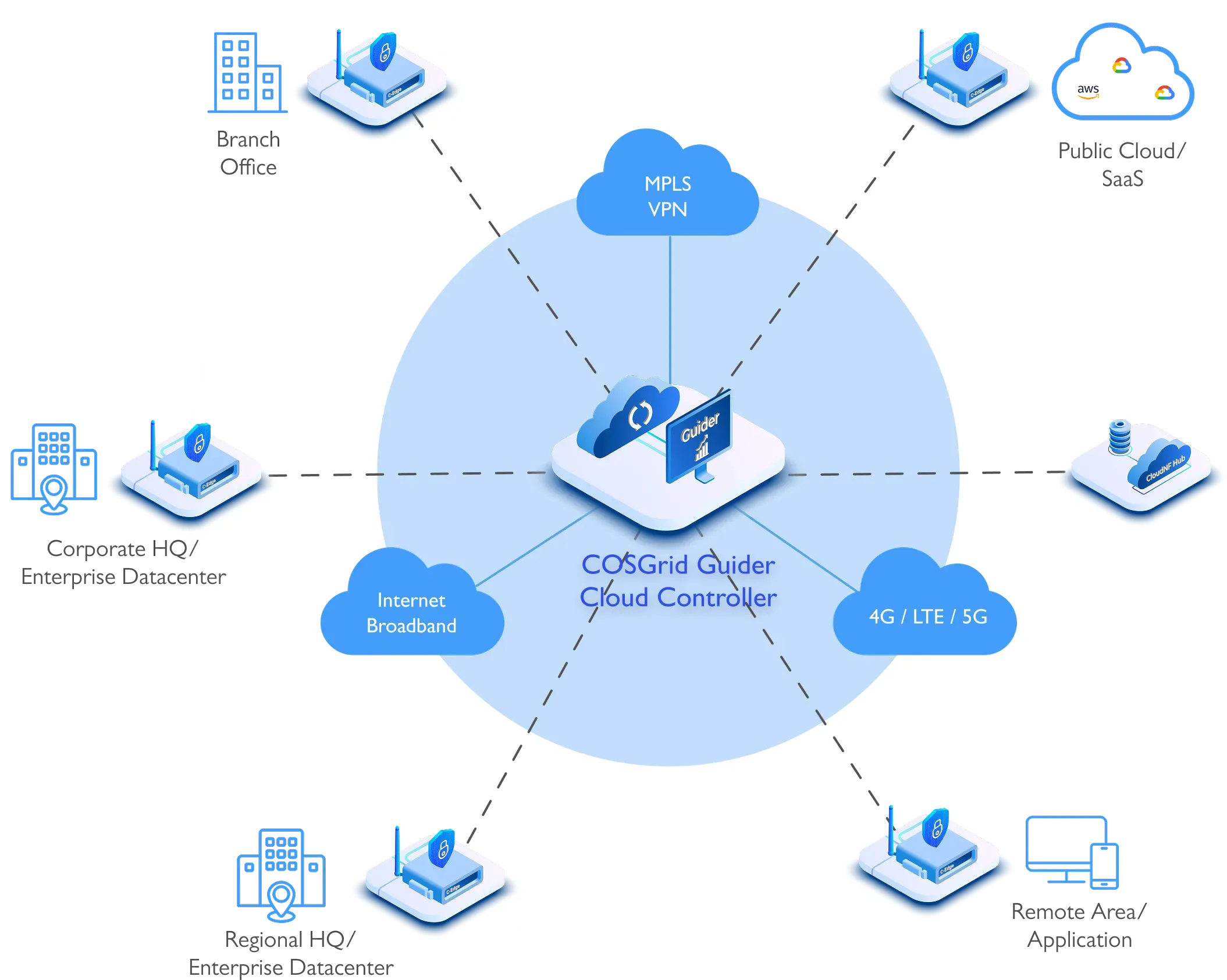
SD-WAN architecture consists of three primary components that work together to deliver intelligent, software-controlled wide area networking:
Components of SD-WAN Architecture

Centralized Orchestrator
A cloud-based, multi-tenant management plane that provides unified control of all SD-WAN edges and gateways. The orchestrator pushes configuration, traffic, tunnel, and QoS policies to edge devices automatically, eliminating manual per-branch configuration.

SD-WAN Edge
A physical or virtual appliance deployed at each branch location. SD-WAN edges support zero-touch provisioning: each device is pre-assigned a unique ID and authenticates via hardware fingerprint and RSA certificate before a secure management tunnel is established. No on-site IT staff is required for deployment.

Cloud Services Gateway
A multi-tenant services edge deployed in cloud PoPs to provide direct, optimized connectivity between branches and cloud platforms (AWS, Azure, SaaS applications) without backhauling traffic through the data center.
Device On-Boarding & Security
- Each SD-WAN device is pre-assigned a unique ID and secret key by the orchestrator.
- Devices authenticate using hardware fingerprints and receive an RSA certificate.
- Upon registration, a secure management tunnel is established, and traffic, tunnel, and QoS policies are pushed.
Core Features of SD-WAN
- Unified Transport: Multiple active WAN links with dynamic link quality assessment.
- Smart Traffic Steering: Application-based routing and multi-path bonding.
- Integrated Security: Scalable VPN and basic UTM features.
- Centralized Orchestration: Simplifies operations and service management.
- Flexible Deployment: Physical or virtual SD-WAN edges.
- Service Orchestration: Full lifecycle management for SD-WAN and related services.
- Subscriber Portal: Enables easy service ordering and modification.
07 — Comparison
SD-WAN vs Traditional WAN: A Side-by-Side Comparison for Enterprise Decision-Makers
Traditional WAN and SD-WAN are not mutually exclusive — many enterprises use a hybrid approach. However, understanding the structural differences is critical before making an architectural decision.
MPLS, routers, VPNs — centralized hub-and-spoke
- ✕All branch traffic routes through a central data center before reaching its destination.
- ✕Reliable and predictable, but creates latency for cloud and SaaS applications due to traffic tromboning.
- ✕High bandwidth cost — MPLS circuits are expensive, especially as cloud traffic volumes grow.
- ✕Limited — each new branch requires manual hardware provisioning and physical circuit installation.
- ✕Slow — every QoS update requires manual reconfiguration across all individual branch devices.
- ✕Not designed for cloud-first environments — SaaS traffic must backhaul through the data center.
Software-defined, cloud-ready, flexible
- ✓Centralized software controller manages all WAN traffic across multiple transport links — broadband, LTE, and MPLS simultaneously.
- ✓Dynamic, application-aware path selection routes each workload over the best available link in real time.
- ✓Replaces or augments costly MPLS with broadband and LTE — reducing bandwidth spend while increasing capacity.
- ✓Zero-touch provisioning brings new branches online in hours — no on-site engineers or manual circuit setup required.
- ✓Policy changes propagate automatically across all branch edges from a single orchestration console — instantly.
- ✓Enables direct cloud breakout — SaaS and cloud traffic reaches its destination without data center backhaul.
08 — Security
How Does SD-WAN Provide Network Security? Encryption, Microsegmentation, and vNSF
SD-WAN provides network security through a layered approach that includes IPsec-encrypted tunnels, integrated firewall policies, application-level microsegmentation, and increasingly, virtualized network security functions (vNSF) delivered as software within the SD-WAN fabric.
What SD-WAN secures by default: IPsec has become the baseline standard among enterprise SD-WAN vendors for encrypting branch-to-branch and branch-to-cloud traffic. Application microsegmentation limits lateral movement within the network by isolating workloads into separate policy zones — reducing the risk of a single compromised endpoint affecting the broader network.
What SD-WAN does not replace: SD-WAN security capabilities vary significantly by vendor. Basic SD-WAN provides connectivity-layer security; comprehensive protection requires integration with SASE (Secure Access Service Edge) components such as a Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), and Zero Trust Network Access (ZTNA).
Enterprises increasingly deploy virtualized security functions within SD-WAN to avoid the cost and complexity of separate hardware at each branch — enabling scalable, software-delivered protection that updates centrally without field hardware replacements.
09 — Concepts
SDN vs SD-WAN: What Is the Difference?
SDN (Software-Defined Networking) and SD-WAN (Software-Defined Wide Area Network) share the same foundational principle — separating the control plane from the data plane — but they operate at different network scopes and solve different problems.
SDN applies software-defined control to local area networks and data centers. It decouples network intelligence from physical switches and routers within a campus or data center environment, enabling centralized, programmable control of internal traffic flows.
SD-WAN applies the same software-defined principles to wide area networks — the connections between geographically distributed branch offices, data centers, and cloud environments. Where SDN manages traffic within a site, SD-WAN manages traffic between sites.
In practice, SD-WAN can be seen as the WAN extension of SDN philosophy: both abstract network control into software, but SD-WAN specifically addresses multi-site enterprise connectivity at internet scale.
10 — Comparison
SD-WAN vs MPLS: Cost, Performance, Security, and When to Use Each
MPLS and SD-WAN are not direct replacements — they serve different roles in enterprise WAN strategy. The right choice depends on performance requirements, cost tolerance, and cloud adoption stage.
MPLS strengths: guaranteed packet delivery, consistent low-latency QoS, and strong traffic prioritization for real-time applications (VoIP, video conferencing). MPLS operates on a private provider network, avoiding public internet variability.
MPLS limitations: high per-Mbps bandwidth cost (particularly for data-heavy modern workloads), inflexible provisioning timelines, limited scalability, and no native encryption — meaning MPLS traffic can be exposed if provider infrastructure is compromised.
SD-WAN strengths: significantly lower cost by leveraging broadband and LTE alongside or instead of MPLS; built-in IPsec encryption; centralized orchestration; dynamic multi-path routing; and cloud-first design with native SaaS optimization.
Recommended approach: Most enterprises adopt a hybrid strategy — retaining MPLS for latency-sensitive, business-critical traffic while offloading general internet and SaaS traffic to SD-WAN-managed broadband links. This delivers MPLS-level reliability for critical workloads at a lower aggregate cost.
11 — Comparison
SD-WAN vs VPN
Both SD-WAN and traditional VPN establish encrypted tunnels between remote locations, but they differ fundamentally in intelligence, scalability, and management complexity.
A traditional VPN creates a single encrypted tunnel between two endpoints. Managing VPN at scale requires manual configuration of each tunnel, individual monitoring of tunnel health, and manual failover when a link degrades — making it error-prone and operationally expensive across dozens of branch sites.
SD-WAN automates all of this: it builds redundant encrypted tunnels across multiple active WAN links simultaneously, continuously monitors path quality (latency, jitter, packet loss), and fails over automatically to the best available path — without human intervention. SD-WAN also applies application-aware policies, meaning business-critical applications are always routed over the optimal path, not just any available tunnel.
Key distinction: SD-WAN is not a VPN replacement — it is a WAN management platform that includes VPN as one component, alongside dynamic path selection, centralized orchestration, and application-layer visibility.
12 — Comparison
SD-WAN vs DMVPN: How Dynamic Multipoint VPN Compares to Modern SD-WAN
DMVPN (Dynamic Multipoint VPN) is a Cisco-originated technology that extends IPsec with NHRP (Next Hop Resolution Protocol) and mGRE (Multipoint GRE) tunnels to create a dynamic mesh VPN — allowing spoke sites to communicate directly without routing all traffic through a hub, unlike traditional IPsec site-to-site VPNs.
While DMVPN improves on static IPsec tunnels by enabling dynamic spoke-to-spoke connectivity, it still requires individual configuration of each hub and spoke device. Configuration complexity scales with network size, and DMVPN lacks native application-awareness, centralized orchestration, or real-time link quality monitoring.
SD-WAN vs DMVPN summary:
- Each SD-WAN device is pre-assigned a unique ID and secret key by the orchestrator
- Devices authenticate using hardware fingerprints and receive an RSA certificate
- Upon registration, a secure management tunnel is established, and traffic, tunnel, and QoS policies are pushed
13 — Comparison
SD-WAN vs WAN Optimization: Complementary Technologies, Not Competitors
WAN Optimization and SD-WAN address different dimensions of WAN performance — and are often deployed together rather than as alternatives.
WAN Optimization reduces the volume of data traversing the WAN through techniques including: deduplication (substituting shorthand codes for recurring data patterns to avoid retransmitting redundant content); compression; protocol spoofing; and traffic shaping (QoS) to prioritize latency-sensitive applications over bulk transfers.
SD-WAN focuses on how traffic is routed rather than how much traffic is sent. It accounts for real-time path conditions — jitter, latency, and packet loss — to steer each application to its optimal WAN path. Unlike WAN Optimization, SD-WAN does not reduce data volume, but ensures that traffic reaches its destination via the most reliable and efficient route.
When used together, WAN Optimization reduces the data volume that SD-WAN needs to route — delivering compounded improvements in application performance, particularly for legacy protocols and latency-sensitive enterprise applications running over long-distance WAN links.
14 — Business Case
Does Your Organization Need SD-WAN? 4 Signs It's Time to Migrate
SD-WAN is the right solution for organizations facing one or more of the following conditions:
- Growing cloud and SaaS adoption — If your workforce increasingly relies on Microsoft 365, Salesforce, or other SaaS platforms, backhauling traffic through a central data center over MPLS is creating unnecessary latency. SD-WAN enables direct cloud breakout.
- Rising WAN costs — MPLS bandwidth is expensive relative to broadband. Organizations spending disproportionately on WAN circuits while underutilizing capacity are candidates for SD-WAN cost optimization.
- Branch expansion or remote workforce growth — Traditional WAN provisioning at new sites requires weeks of manual setup. SD-WAN's zero-touch provisioning enables new locations to come online in hours.
- Inadequate network visibility — If your team lacks real-time insight into which applications are consuming bandwidth, or cannot enforce QoS policies centrally, SD-WAN's application-layer telemetry closes that gap.
SD-WAN also delivers built-in integrated security (IPsec, firewall, microsegmentation), a virtual overlay network across all transport types, and a unified management infrastructure for both network and security policies.
15 — Vendor Selection
How to Choose an SD-WAN Vendor: 5 Critical Evaluation Questions
Selecting an SD-WAN vendor requires evaluating both current requirements and long-term scalability. Ask these five questions before committing:
16 — Summary
SD-WAN Key Facts: What You Need to Know
SD-WAN is a software-defined wide area network architecture that virtualizes WAN connectivity, enabling enterprises to manage multiple transport links — broadband, LTE, and MPLS — through a single centralized controller.
Key facts about SD-WAN:
SD-WAN separates the WAN control plane from hardware, delivering network programmability and central management across all branch sites.
Its cloud-native architecture scales horizontally — new branches are onboarded via zero-touch provisioning without on-site configuration.
SD-WAN enables direct cloud breakout, reducing latency for SaaS and cloud applications compared to hub-and-spoke MPLS architectures.
As part of a SASE framework, SD-WAN converges network connectivity with cloud-delivered security — including ZTNA, SWG, and CASB — in a single managed service.